Yesterday two critical server vulnerabilities were discovered that affect nearly every modern server and desktop computer made after 1995. These vulnerabilities known as “Meltdown” and “Spectre” affect Thexyz and many other service providers. Since becoming aware of these vulnerabilities, Thexyz has been working diligently to plan and implement the best resolution for our customers. Our security and development teams have been working with our vendors to deploy the required updates to mitigate vulnerabilities.
What are these vulnerabilities?
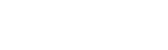
Meltdown and Spectre exploit critical vulnerabilities in modern processors. These hardware bugs allow programs to read data that is
currently processed on the computer. While programs are typically not permitted to read data from other programs, a malicious program can exploit Meltdown and Spectre to get hold of data stored in the memory of other running programs.
Some patches have already been released to mitigate the risks of these vulnerabilities. Based on the requirements of most of these patches, it will be required to reboot customers’ servers. We will be scheduling these reboots, and updating affected customers prior to them taking place.
We are continuing to monitor the situation for further information and will be updating our customers as more information becomes available. Our customers’ security and environments are a top priority, and we can assure you we have the best team working feverishly to fix these vulnerabilities in the least impactful manner.
Who reported Meltdown?
Meltdown was independently discovered and reported by three teams:
- Jann
Horn (Google Project Zero), - Werner Haas, Thomas Prescher (Cyberus Technology),
- Daniel Gruss, Moritz Lipp, Stefan Mangard, Michael Schwarz (Graz University of Technology)
Who reported Spectre?
Spectre was independently discovered and reported by two people:
- Jann Horn (Google Project Zero) and
- Paul Kocher in collaboration with, in alphabetical order,
Daniel Genkin (University of Pennsylvania and University of Maryland), Mike Hamburg (Rambus), Moritz Lipp (Graz University of Technology), and Yuval Yarom (University of Adelaide and Data61)
The vulnerability announcement and applicable white papers are available at:
https://meltdownattack.com/